Enforcing a good password policy on Amazon Linux 2
Set a good password policy on Amazon Linux 2
Using a good password is one of the first steps to a better security practice. The most easiest way to ensure that the users use the best password is to enforce it at the system level.
Following is the command that you can use to ensure that your Amazon Linux 2 server uses a standard password policy.
Password policy
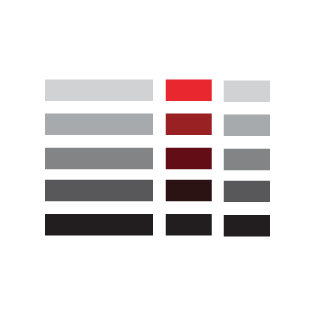
| Policy | Description |
|---|---|
| Character set | Alphanumeric characters, special symbols, or a combination of all three |
| Password length | 14 characters or more |
| Password expiry | None |
| Password reuse | None |
| Account lock | Account will be locked for 30 minutes after 6 failed login attempts |
Command
The following command will set the above password policy on the server.
sudo authconfig --passminlen=14 --enablefaillock --faillockargs="deny=6 unlock_time=1800" --passminclass=4 --updateVerification
You can verify that the above password policy is implemented by checking the system-auth configuration file. Please note that changing this file directly will not be persistent since the changes will be reverted when the authconfig command is run again with a different configuration.
cat /etc/pam.d/system-auth#%PAM-1.0
# This file is auto-generated.
# User changes will be destroyed the next time authconfig is run.
auth required pam_env.so
auth required pam_faildelay.so delay=2000000
auth required pam_faillock.so preauth silent deny=6 unlock_time=1800
auth sufficient pam_unix.so nullok try_first_pass
auth requisite pam_succeed_if.so uid >= 1000 quiet_success
auth required pam_faillock.so authfail deny=6 unlock_time=1800
auth required pam_deny.so
account required pam_faillock.so
account required pam_unix.so
account sufficient pam_localuser.so
account sufficient pam_succeed_if.so uid < 1000 quiet
account required pam_permit.so
password requisite pam_pwquality.so try_first_pass local_users_only retry=3 authtok_type=
password sufficient pam_unix.so sha512 shadow nullok try_first_pass use_authtok
password required pam_deny.so
session optional pam_keyinit.so revoke
session required pam_limits.so
-session optional pam_systemd.so
session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid
session required pam_unix.soReferences
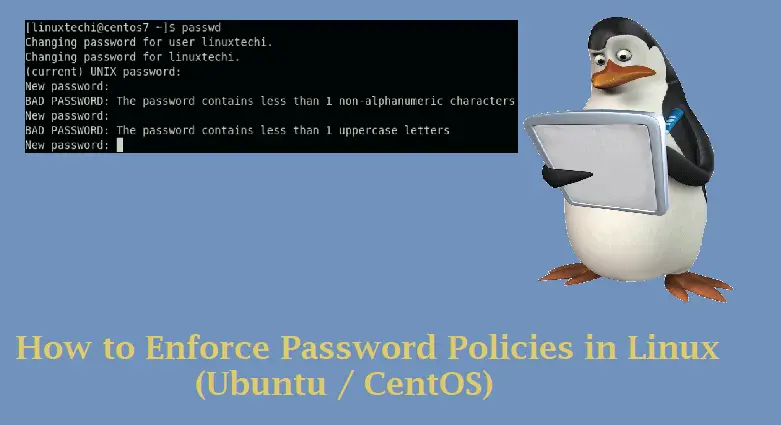
How to Enforce Password Policies in Linux (Ubuntu / CentOS)
In this guide we will learn how to enforce password policies in Linux based operating systems like CentOS, RHEL, Ubuntu and Debian.
authconfig(8) - Linux man page
authconfig provides a simple method of configuring /etc/sysconfig/network to handle NIS, as well as /etc/passwd and /etc/shadow, the files used for shadow password support.
Lock User Account After n Failed Login attempts in Linux
Learn how to lock user accounts automatically after n incorrect or failed login attempts in Linux distributions like CentOS, RHEL, Fedora, Debian and Ubuntu.
How to enable faillock using authconfig - Red Hat Customer Portal
Executing authconfig command removes the faillock entries from PAM files. Configure faillock for persistent settings in PAM files.

CentOS 7 : Set Password Rules : Server World
How to set password complexity in redhat 7.5?
I am trying to set a password policy complexity on red-hat 7.5.i want that every user that will try to change his password will have to use password with at least - (1 Lower , 1 Upper , 1 Digit , 1